��Ϊusg6300����ǽ���ͨ���������������������������ˣ����ڷ���ǽ���ֹ��ϻ�����ж�����
��Ϊusg6300����ǽ��ͨ���������������������������ˣ����ڷ���ǽ���ֹ��ϻ�����ж����⣬����ǽ�����������������ȥ���ã�
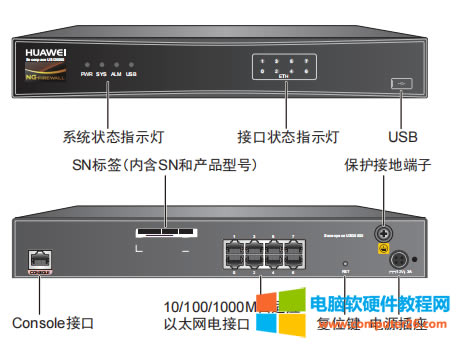
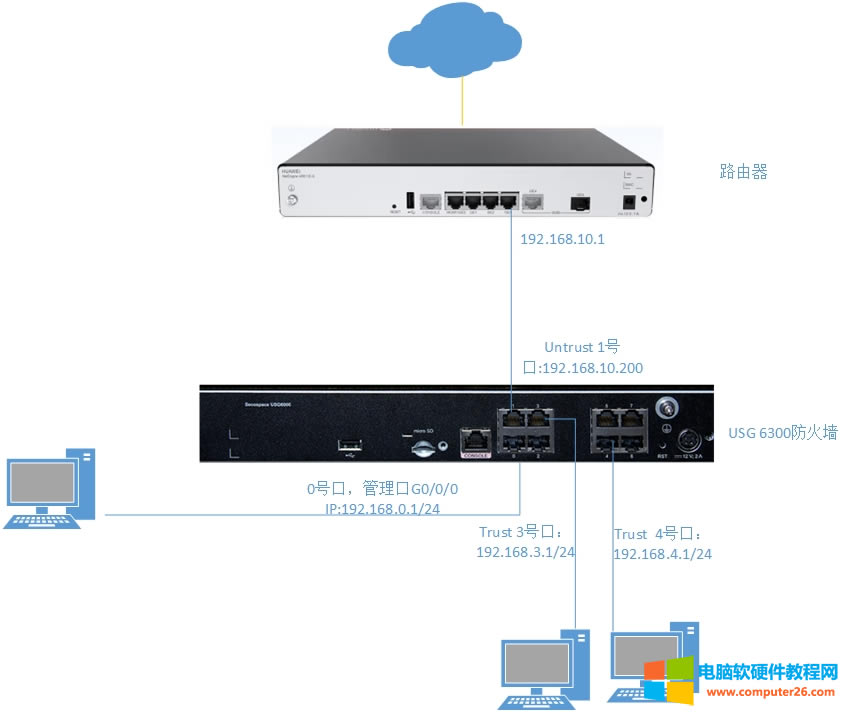
��ͼ��ʾ������ǽӲ���豸��


����ǽ��������������á�
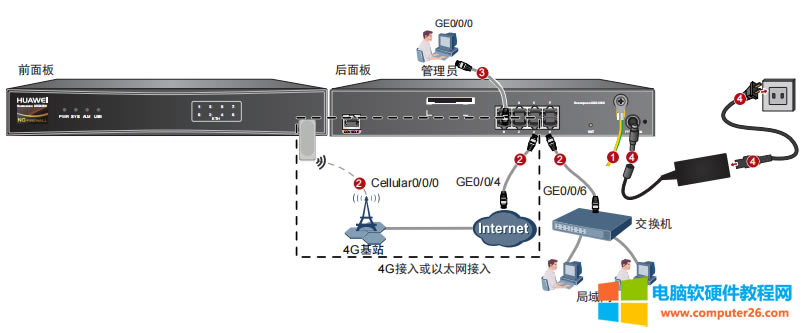
����ǽ�Ļ�����������ͼ��
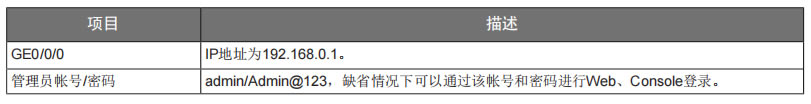
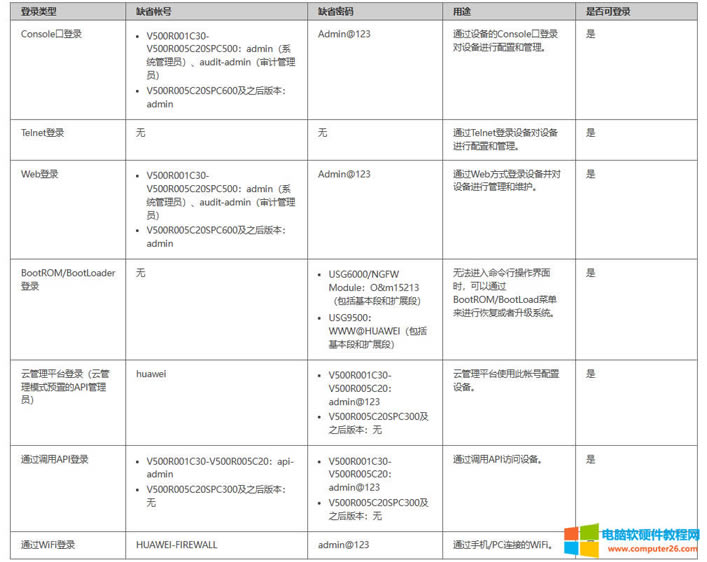
����ǽ��Ĭ�Ϲ���IP��ַ����Ĭ���ʺź����롣
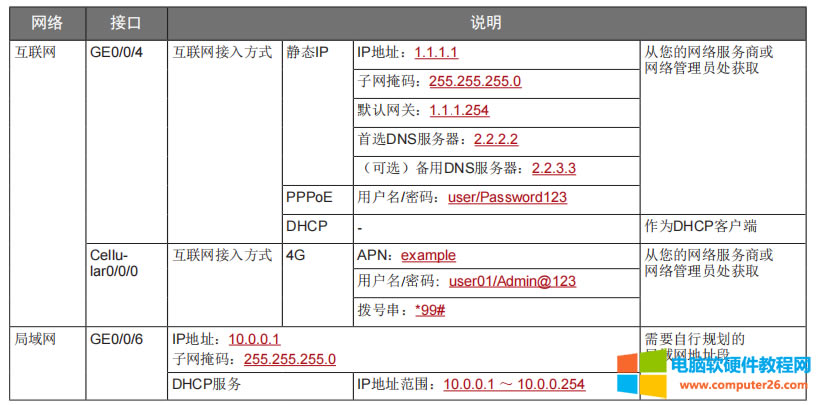
�����Ŀ������ù滮����
Ĭ���������
��������
��Ϊ����ǽ�������ù���
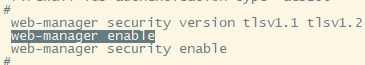
1.��˵����ʹ������ȥ���Ի�Ϊ�ķ���ǽ���������ǻ�����Ҫ��web����ģ�ʹ��web-manager enable����������ǽ��web���档
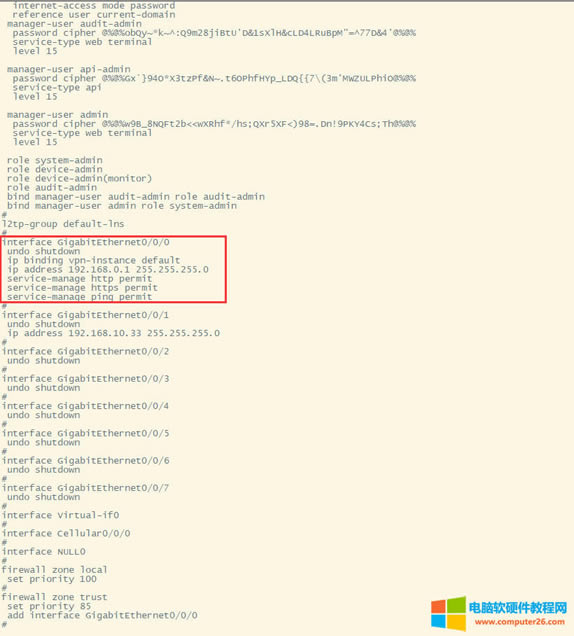
2.�鿴һ�·���ǽ���������ã����Կ�����ǰ��G0/0/0�ſ�IP��ַ��Ĭ�ϵ�192.168.0.1/24������Ĭ�Ͽ�����http��https��¼��������ping��
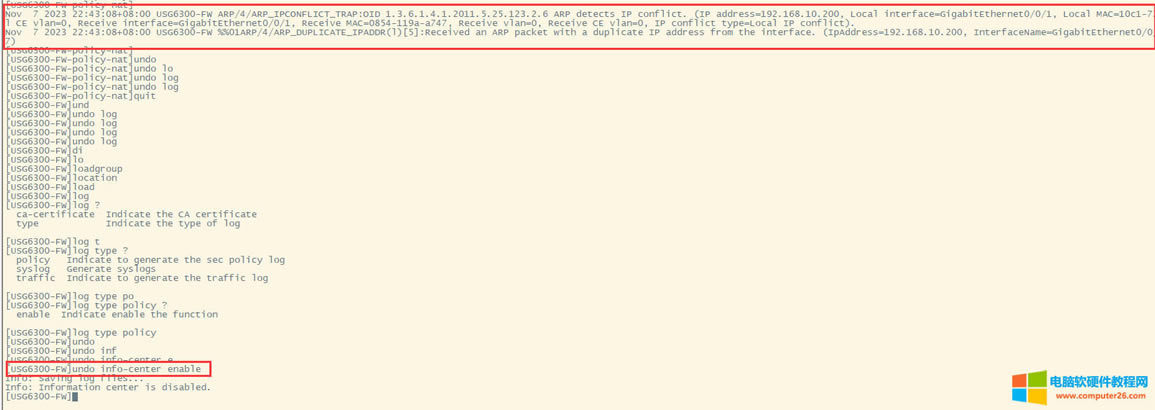
3.����������ʱ���ر�log��Ӧ�����������������˳����ʹ��undo info-center enable���ر�log��־��
4.���ַ���ǽ�Ľӿ�������Ϊ����ǽ�ǽӿڷ�����ģ���֮ǰ������������ϸ�������ǽ�Ľӿ����֣�����Ȥ�Ŀ��Բο���С��Ҳ�ܿ��Ķ����������ǽ������ƪ
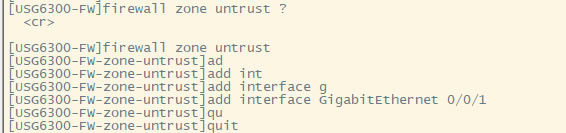
��G0/0/1���ֵ��������ӽӿڣ�Untrsut��
ʹ��zone untrust���뵽untrust����Ȼ��ʹ��add���ӽӿڵ�untrust����
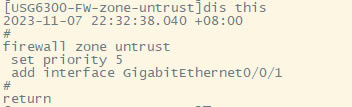
�������֮�鿴���ã����Կ������ȼ���Ĭ�ϵ����þ���5�����Կ���Untrust�����Ѿ�������һ���ӿ���G0/0/1��
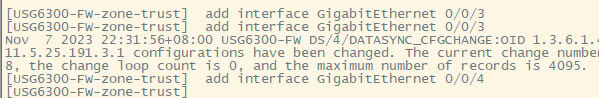
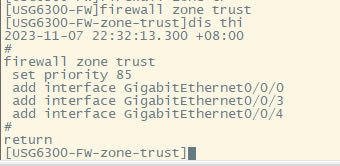
��G0/0/3��G0/0/4���ӵ�Trust����
ʹ��zone trust���뵽trust����Ȼ����ʹ��add���ӽӿڵ���������
�������֮�鿴Trust�������ã����Կ���Ĭ�ϵ�trust��������ȼ���85��������һ��G0/0/0��Ĭ�����ӵ�Trust����ģ����������ӿ����ֶ����ӽ����ġ�
5.DHCP����
Ϊ3��������DHCP���ܣ���������ϸ�˽�DHCP������õģ���ο���ʲô�㻹�����������У�ȥ���û�Ϊ����ǽ��DHCP����
ip pool dhcp1
gateway-list 192.168.10.1 192.168.3.1
network 192.168.3.0 mask 255.255.255.0
excluded-ip-address 192.168.3.200 192.168.3.254
lease unlimited
dns-list 114.114.114.114
6.���ýӿ�IP��ַ����˾����Ҫ���������Σ�һ����192.168.3.0/24���Σ�һ����192.168.4.0/24���Ρ�
���������ã�untrust���ӿ����ã�
interface GigabitEthernet0/0/1
undo shutdown
ip address 192.168.10.200 255.255.255.0
�����ڣ�trust���������ӿ����ã�
�����������ڣ�Ϊ��ά�����㣬ֱ�ӽ����й�������������
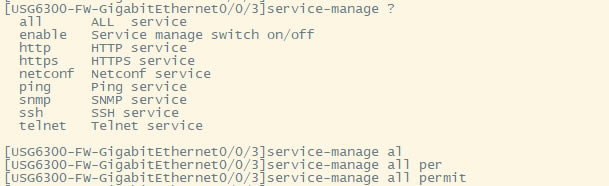
service-manage all permit--��������Э���¼
����G0/0/3 IP��ַ��
interface GigabitEthernet0/0/3
undo shutdown
ip address 192.168.3.1 255.255.255.0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
service-manage netconf permit
dhcp select global--ʹ�õ�ȫ��DHCP���ܡ�
G0/0/4�ӿ����õ��ǽӿ�DHCP����
interface GigabitEthernet0/0/4
undo shutdown
ip address 192.168.4.1 255.255.255.0
dhcp select interface
dhcp server excluded-ip-address 192.168.4.2 192.168.4.20
dhcp server dns-list 218.2.135.1
7.����NAT����
ʹ��Nat-Policy������뵽NAT���������С���Ϊ�������ֻ��һ�������ڣ�������Ĭ�Ͻ�������ת�������ɣ���������easy-IP�����������������ת���������ڣ�Untrust�ӿ�IP��ַ��
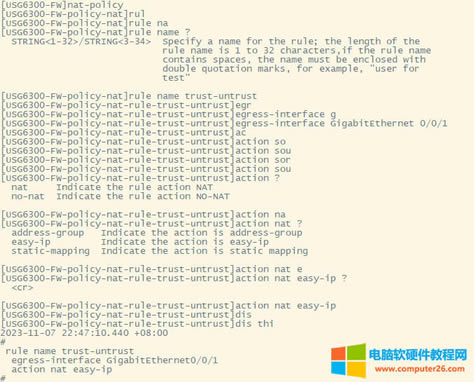
[USG6300-FW]nat-policy
[USG6300-FW-policy-nat]rule name trust-untrust---����һ��Nat���ԵĹ���
[USG6300-FW-policy-nat-rule-trust-untrust]egress-interface GigabitEthernet 0/0/1-----������������G0/0/1�ӿڣ�Ӣ[?i?��res]���ڡ����
[USG6300-FW-policy-nat-rule-trust-untrust]action nat easy-ip---�������û���Դ��ַת��Ϊ�����ӿڵĵ�ַ
[USG6300-FW-policy-nat-rule-trust-untrust]dis thi--�������֮�鿴nat����
2023-11-07 22:47:10.440+08:00
#
rule name trust-untrust
egress-interface GigabitEthernet0/0/1
action nat easy-ip
#
return
8.��ȫ������У��ڷ���ǽ��һ�����ĸ��ӿ�����untrust��trust��dmz��local����ͬ����֮ǰͨ�ţ�����Ҫ���ڷ���ǽ�����ð�ȫ���ԣ��������ֹ��ͬ����֮����������ʡ�
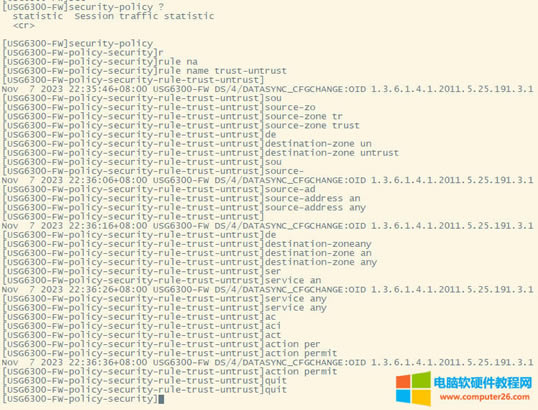
[USG6300-FW]security-policy---���밲ȫ����
[USG6300-FW-policy-security]rule name trust-untrust---����������trust����ȥ��untrst
[USG6300-FW-policy-security-rule-trust-untrust]source-zone trust---Դ������trust
[USG6300-FW-policy-security-rule-trust-untrust]destination-zone untrust---Ŀ��������untrust
[USG6300-FW-policy-security-rule-trust-untrust]source-address any--Դ�ص�ַ���κ�IP��ַ
[USG6300-FW-policy-security-rule-trust-untrust]destination-zone any---Ŀ������Ҳ���κε�ַ��
[USG6300-FW-policy-security-rule-trust-untrust]service any---���ʵķ���Ҳ���κη���
[USG6300-FW-policy-security-rule-trust-untrust]action permit---��������������
[USG6300-FW-policy-security-rule-trust-untrust]quit---�˳�
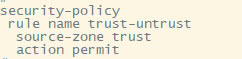
[USG6300-FW-policy-security]dis thi---�鿴����
2023-11-07 22:37:23.830+08:00
#
security-policy
rule name trust-untrust
source-zone trust
action permit
#
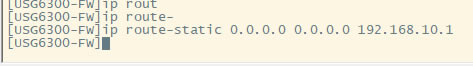
9.����Ĭ��·��
ip route-static 0.0.0.0 0.0.0.0 192.168.10.1
��������������Ĭ��·�ɣ�������δ֪Ŀ�ĵص��������͵�ָ�������ص�ַ��192.168.10.1����
10.��ʱ����������ӵ�G0/0/3�ڣ����Զ���ȡһ��IP��ַ����������������
11�����õ�����
<USG6300-FW>display current-configuration
2023-11-07 22:55:50.970+08:00
!Software Version V500R001C60SPC300
#
sysname USG6300-FW
#
l2tp domain suffix-separator
#
undo info-center enable
#
authentication-profile name portal_authen_default
#
ipsec sha2 compatible enable
#
undo factory-configuration prohibit
#
undo telnet server enable
undo telnet ipv6 server enable
#
clock timezone Beijing add 08:00:00
#
firewall detect ftp
#
firewall defend action discard
#
log type traffic enable
log type syslog enable
log type policy enable
#
undo dataflow enable
#
undo sa force-detection enable
#
isp name"china mobile"set filename china-mobile.csv
isp name"china unicom"set filename china-unicom.csv
isp name"china telecom"set filename china-telecom.csv
isp name"china educationnet"set filename china-educationnet.csv
#
user-manage web-authentication security port 8887
password-policy
level high
user-manage single-sign-on ad
user-manage single-sign-on tsm
user-manage single-sign-on radius
user-manage auto-sync online-user
page-setting
user-manage security version tlsv1.1 tlsv1.2
#
firewall ids authentication type aes256
#
web-manager security version tlsv1.1 tlsv1.2
web-manager enable
web-manager security enable
#
firewall dataplane to manageplane application-apperceive default-action drop
#
dhcp enable
#
update schedule ips-sdb daily 23:51
update schedule av-sdb daily 23:51
update schedule sa-sdb daily 23:51
update schedule cnc daily 23:51
update schedule file-reputation daily 23:51
#
ip vpn-instance default
ipv4-family
#
time-range worktime
period-range 08:00:00 to 18:00:00 working-day
#
ike proposal default
encryption-algorithm aes-256 aes-192 aes-128
dh group14
authentication-algorithm sha2-512 sha2-384 sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
web-auth-server default
port 50100
#
portal-access-profile name default
#
ip pool dhcp1
gateway-list 192.168.10.1 192.168.3.1
network 192.168.3.0 mask 255.255.255.0
excluded-ip-address 192.168.3.200 192.168.3.254
lease unlimited
dns-list 114.114.114.114
#
aaa
authentication-scheme default
authentication-scheme admin_local
authentication-scheme admin_radius_local
authentication-scheme admin_hwtacacs_local
authentication-scheme admin_ad_local
authentication-scheme admin_ldap_local
authentication-scheme admin_radius
authentication-scheme admin_hwtacacs
authentication-scheme admin_ad
authentication-scheme admin_ldap
authorization-scheme default
accounting-scheme default
domain default
service-type internetaccess ssl-vpn l2tp ike
internet-access mode password
reference user current-domain
manager-user audit-admin password cipher % %obQy~*k~^:Q9m28jiBtU'D&1sXlH&cLD4LRuBpM"=^77D&4' % %
service-type web terminal
level 15
manager-user api-admin password cipher % %Gx`}94O*X3tzPf&N~.t6OPhfHYp_LDQ{{7\
3m'MWZULPhiO % %
service-type api
level 15
manager-user adminpassword cipher % %yW9x%WZ
z"hm[>T=85R>fsE`hi%w5mvXG<ugJX0*Sc;2sEcf % %
service-type web terminal
level 15
role system-admin
role device-admin
role device-admin
monitor
role audit-admin
bind manager-user audit-admin role audit-admin
bind manager-user admin role system-admin
#
interface Vlanif1
dhcp select global
#
l2tp-group default-lns
#
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 192.168.0.1 255.255.255.0
service-manage http permit
service-manage https permit
service-manage ping permit
#
interface GigabitEthernet0/0/1
undo shutdown
ip address 192.168.10.200 255.255.255.0
#
interface GigabitEthernet0/0/2
undo shutdown
#
interface GigabitEthernet0/0/3
undo shutdown
ip address 192.168.3.1 255.255.255.0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
service-manage netconf permit
dhcp select global
#
interface GigabitEthernet0/0/4
undo shutdown
ip address 192.168.4.1 255.255.255.0
dhcp select interface
dhcp server excluded-ip-address 192.168.4.2 192.168.4.20
dhcp server dns-list 218.2.135.1
#
interface GigabitEthernet0/0/5
undo shutdown
#
interface GigabitEthernet0/0/6
undo shutdown
#
interface GigabitEthernet0/0/7
portswitch
undo shutdown
port link-type access
#
interface Virtual-if0
#
interface Cellular0/0/0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet0/0/3
add interface GigabitEthernet0/0/4
#
firewall zone untrust
set priority 5
add interface GigabitEthernet0/0/1
#
firewall zone dmz
set priority 50
#
api
#
ip route-static 0.0.0.0 0.0.0.0 192.168.10.1
#
undo ssh server compatible-ssh1x enable
#
user-interface con 0
authentication-mode aaa
user-interface vty 0 4
authentication-mode aaa
protocol inbound ssh
user-interface vty 16 20
#
pki realm default
undo crl auto-update enable
#
sa
#
location
#
nat address-group 3test 1
mode pat
#
multi-interface
mode proportion-of-weight
#
right-manager server-group
#
agile-network
#
device-classification
device-group pc
device-group mobile-terminal
device-group undefined-group
#
user-manage server-sync tsm
#
security-policy
rule name trust-untrust
source-zone trust
action permit
#
auth-policy
#
traffic-policy
#
policy-based-route
#
nat-policy
rule name trust-untrust
egress-interface GigabitEthernet0/0/1
action nat easy-ip
#
proxy-policy
#
quota-policy
#
pcp-policy
#
dns-transparent-policy
mode based-on-multi-interface
#
rightm-policy
#
sms
#
return
<USG6300-FW>