互联网用户访问防火墙DMZ内服务器设置演示
前面二节我们讨论了在防火墙网络中,内网用户访问DMZ区域的服务器,以及内网用户访问互联网的配置;
当然了我们架设服务器的目的不仅是服务于内部用户,有时我们在外部也需要访问内部服务器,同时我们提供WEB服务为其他所有的用户。
今天我们就说说如何为外部用户提供服务。
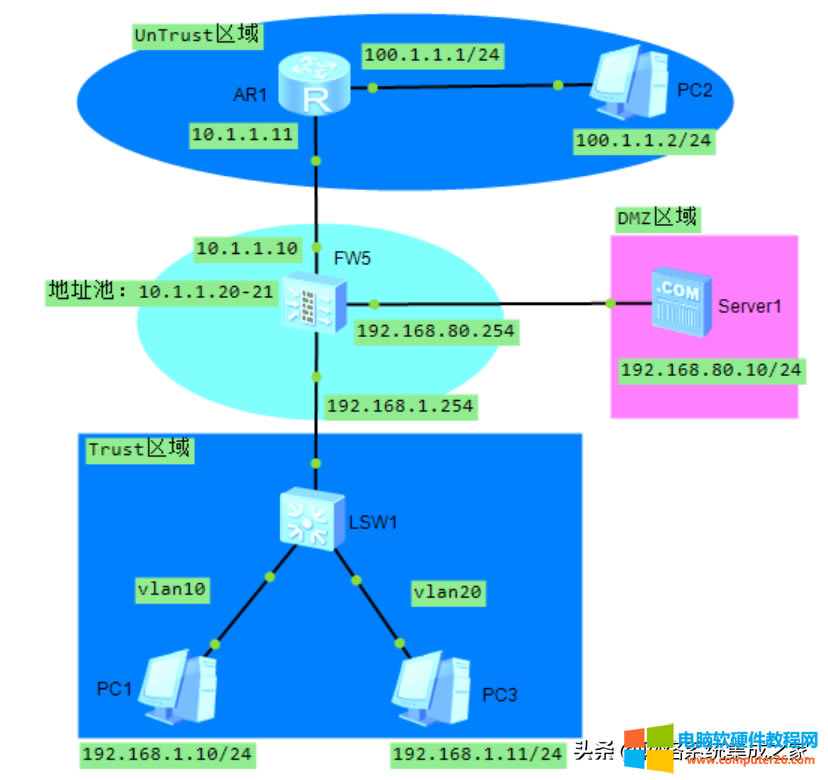
如上图,互联网用户PC2如何才能访问DMZ区域的Server1呢?
一、配置DMZ访问互联网UnTrust区域
[FW1]nat-policy interzone dmz untrust outbound
[FW1-nat-policy-interzone-dmz-untrust-outbound]policy 20
[FW1-nat-policy-interzone-dmz-untrust-outbound-20]action source-nat
[FW1-nat-policy-interzone-dmz-untrust-outbound-20]address-group 1
[FW1-nat-policy-interzone-dmz-untrust-outbound-20]q
[FW1-nat-policy-interzone-dmz-untrust-outbound]q
[FW1]policy interzone dmz untrust outbound
[FW1-policy-interzone-dmz-untrust-outbound]policy 15
[FW1-policy-interzone-dmz-untrust-outbound-15]action permit
[FW1-policy-interzone-dmz-untrust-outbound-15]q
[FW1-policy-interzone-dmz-untrust-outbound]q
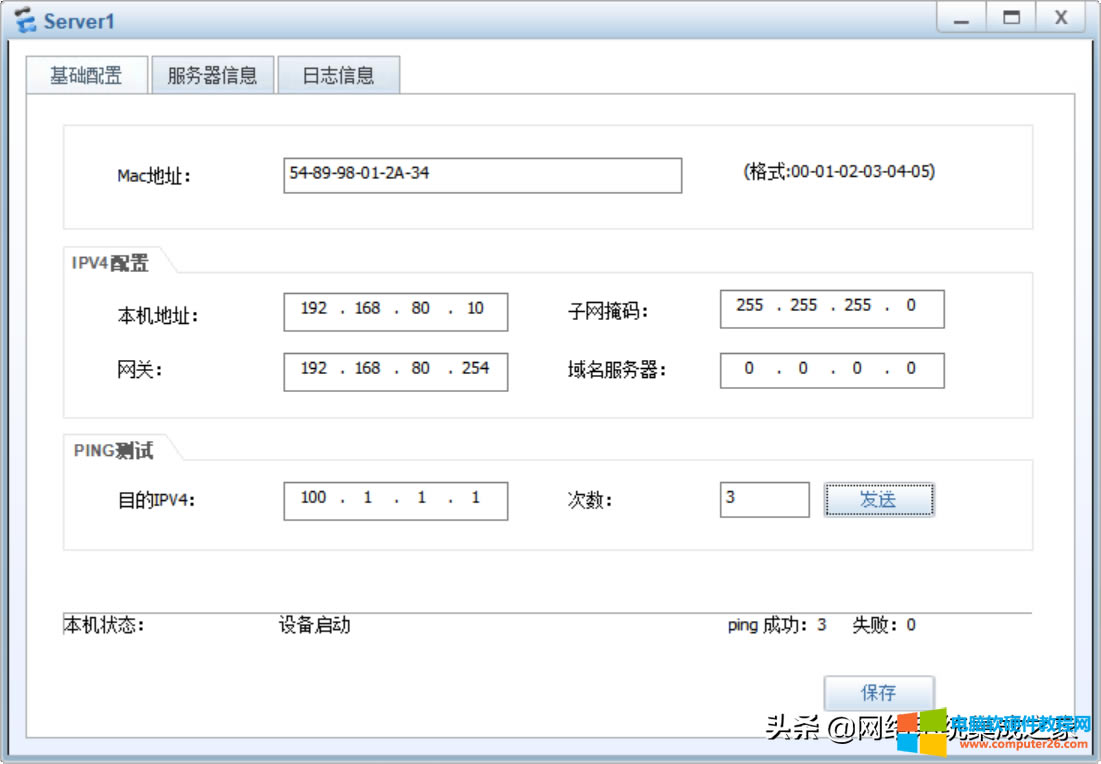
测试
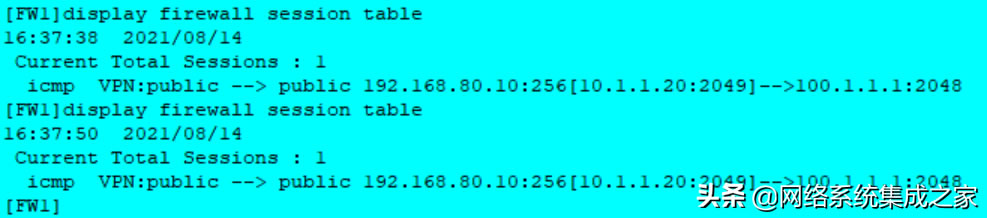
查看NAT转换信息
二、配置公网PC2访问DMZ内服务器
配置静态NAT,实现内网服务器的发布;
[FW1]nat server global 10.1.1.22 inside 192.168.80.10
下列命令,将内部服务器的80端口映射到公网地址80端口上。
[FW1]nat server zone untrust protocol tcp global 10.1.1.22 80 inside 192.168.80.10 80
再配置Untrust区域访问DMZ的包过滤;
[FW1]policy interzone untrust dmz inbound
[FW1-policy-interzone-dmz-untrust-inbound]policy 20
[FW1-policy-interzone-dmz-untrust-inbound-20]policy source 100.1.1.2 0
//本命令表示只允许100.1.1.2主机访问服务器,一般不配置,或者配置成policy source any
[FW1-policy-interzone-dmz-untrust-inbound-20]policy destination 192.168.80.10 0
[FW1-policy-interzone-dmz-untrust-inbound-20]policy service service-set http
[FW1-policy-interzone-dmz-untrust-inbound-20]policy service service-set ftp
[FW1-policy-interzone-dmz-untrust-inbound-20]action permit
[FW1-policy-interzone-dmz-untrust-inbound-20]policy service service-set icmp